Why Doesn’t the C Standard Library Include a Map?
To understand the absence of a standard map, we must first appreciate the principles upon which C was built. C is a low-level, procedural language designed to be minimal, efficient, and close to the hardware. Its standard library reflects this, providing fundamental tools rather than high-level, abstract data structures.
The Philosophy of Minimalism and Control
C’s ethos is to provide the programmer with building blocks and complete control over system resources, especially memory. A complex data structure like a map would inherently hide the details of its memory allocation, resizing, and management. This level of abstraction runs counter to the C philosophy, which trusts the programmer to manage memory explicitly using functions like malloc(), calloc(), and free().
The Challenge of Generics
Modern map implementations are typically generic, meaning they can store keys and values of any data type. C lacks native support for generics. While this can be simulated using void* pointers and function pointers, it adds significant complexity and removes type safety. Including a single, official map implementation in the standard library that could handle all data types gracefully and safely would be a formidable challenge.
Performance Over Convenience
The C standard library prioritizes predictable performance. A generic map implementation’s performance can vary based on the hash function used, the quality of the data keys, and the chosen collision resolution strategy. By leaving the implementation to the developer, C allows for a bespoke solution tailored to the specific performance requirements of the application.
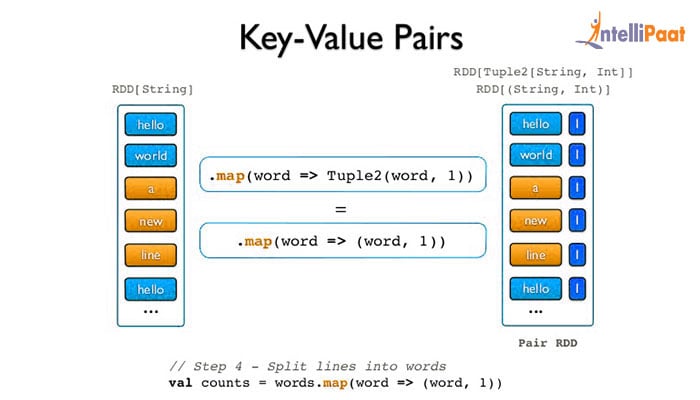
The Core Concept: Associative Arrays and Key-Value Pairs
Before we build one, let’s solidify our understanding of what a map is. A map is an associative array, a data structure that stores a collection of (key, value) pairs. Unlike a traditional C array, which is indexed by sequential integers (0, 1, 2, …), a map is indexed by its keys.
- Insert: Add a new key-value pair to the collection.
- Lookup/Search: Retrieve the value associated with a given key.
- Delete: Remove a key-value pair from the collection based on its key.
The efficiency of these operations is the hallmark of a good map implementation. The goal is to achieve an average time complexity of O(1), or constant time, for each operation.
The Premier Solution: Building a Map with a Hash Table
The most common and efficient way to implement a map in C is by using a hash table. A hash table is a data structure that combines the random access of an array with the flexibility of a linked list to create a powerful key-value store.
What is a Hash Table?
At its core, a hash table is an array of ‘buckets’. The magic lies in the hash function, a special function that takes a key as input and computes an integer index. This index determines which bucket the key-value pair should be stored in. A well-designed hash function distributes keys evenly across the array, minimizing collisions and ensuring fast lookups.
The Inevitability of Collisions
A ‘collision’ occurs when two different keys produce the same hash index. Since the number of possible keys is often far greater than the number of buckets, collisions are inevitable. Therefore, a robust hash table must have a strategy for resolving them.
The most popular collision resolution strategy is Separate Chaining. In this method, each bucket in the array is not a single slot but rather the head of a linked list. When a collision occurs, the new key-value pair is simply added to the linked list at that index. To find an element, you first hash the key to find the correct bucket and then traverse the linked list in that bucket to find the matching key.
Step 1: Defining the Data Structures
To implement a hash table with separate chaining in C, we need two primary structs. First, a node for the linked list to store the key-value pair and a pointer to the next node.
// A node in the linked list for a given bucket
typedef struct KeyValuePair
char* key;
void* value; // Use void* for generic values
struct KeyValuePair* next;
KeyValuePair;Second, we need a structure to represent the hash table itself, which contains the array of buckets (i.e., pointers to KeyValuePair nodes) and its size.
// The hash table structure
typedef struct HashTable
KeyValuePair** buckets;
size_t size;
HashTable;Step 2: The Hash Function
A good hash function is crucial for performance. It should be fast to compute and distribute keys uniformly. For string keys, the ‘djb2’ algorithm is a simple and effective choice.
// A simple string hashing function (djb2)
unsigned long hash_function(const char* str)
unsigned long hash = 5381;
int c;
while ((c = *str++))
hash = ((hash << 5) + hash) + c; /* hash * 33 + c */
return hash;
Step 3: Core Functionality – Insert, Lookup, Delete
- Take a key and a value as input.
- Use the hash function to compute an index for the key:
index = hash_function(key) % table_size. - Traverse the linked list at
buckets. If the key already exists, update its value. - If the key does not exist, create a new
KeyValuePairnode, allocate memory for the key and value, and add it to the front of the linked list.
A lookup operation follows a similar path: hash the key to find the bucket, then traverse the linked list, comparing keys until a match is found. If the end of the list is reached without a match, the key is not in the table.
A delete operation involves finding the node via hash and traversal, then carefully removing it from the linked list by updating the next pointer of the previous node and freeing the memory allocated for the deleted node and its key/value.
Step 4: Memory Management
Proper memory management is paramount in C. Every malloc must have a corresponding free. When inserting, you must allocate memory for the KeyValuePair struct and also for the key string itself (using strdup is a good practice). When deleting a pair, you must free the key and the struct. Finally, you need a function to destroy the entire hash table, which iterates through all buckets, frees every node in every linked list, frees the bucket array itself, and finally frees the HashTable struct.
Alternative Implementations for Map Functionality
While hash tables are the most common approach, they are not the only one. Depending on your specific needs, other data structures can also serve as maps.
Balanced Binary Search Trees (BSTs)
A self-balancing binary search tree, such as a Red-Black Tree or an AVL Tree, can be used to implement a map. Instead of hashing, keys are stored in a sorted order.
Pros: Operations are a guaranteed worst-case O(log n), which can be better than a hash table’s worst-case O(n) (in the case of many collisions). BSTs also allow for ordered traversal of keys, which hash tables do not.
Cons: Implementations are significantly more complex than hash tables. The average-case performance of O(log n) is slower than a hash table’s O(1).
Simple Arrays or Linked Lists
For very small datasets, you could implement a map using a simple dynamic array or a linked list of key-value pairs. To find an element, you would simply iterate through the collection until you find a matching key. However, this approach has a time complexity of O(n) for lookups, making it highly inefficient for anything but the smallest number of elements.
Leveraging Third-Party Libraries
Building a robust, efficient, and bug-free hash table from scratch is a rewarding but time-consuming exercise. For production applications, it is often wiser to use a well-tested, open-source library.
- uthash.h: A fantastic and widely used header-only library. You simply include the header file and then use a set of C macros to add hash table functionality directly to your own structs. It’s fast, easy to integrate, and requires no separate linking.
- GLib: A core library for the GNOME desktop environment, GLib provides a rich set of data structures for C programming, including a powerful `GHashTable`. It is a mature, feature-rich, and highly stable option, though it does add a larger dependency to your project.
Using a library frees you from worrying about the nuances of hash function design and collision resolution, allowing you to focus on your application’s core logic.
Practical Use Cases for Maps in C
- Configuration Parsers: Reading settings from a file (e.g., an `.ini` file) and storing them in a map where the key is the setting name and the value is its configured value.
- Symbol Tables: In compilers and interpreters, a symbol table is a map used to store information about identifiers like variable names and function names.
- Caching: Implementing an in-memory cache where keys represent a request (e.g., a URL) and values represent the response, allowing for rapid retrieval of frequently accessed data.
- Frequency Counting: Processing text or data to count the occurrences of each unique item, storing the item as the key and its count as the value.
Conclusion: Charting Your Course
While C does not provide a map in its standard library, it provides all the necessary tools to build one. The absence of this high-level structure is a feature, not a bug, upholding C’s philosophy of programmer control, minimalism, and performance.
By understanding the principles of hash tables—hash functions, buckets, and collision resolution—you can build a highly efficient map tailored to your specific needs. For those seeking a quicker or more robust solution, trusted third-party libraries like uthash.h offer a powerful alternative.
You now have a complete map for navigating key-value data structures in C. Whether you choose to build your own from scratch or leverage an existing library, you are well-equipped to handle any programming task that requires the power and flexibility of an associative array.